Project Manage With Microsoft Planner
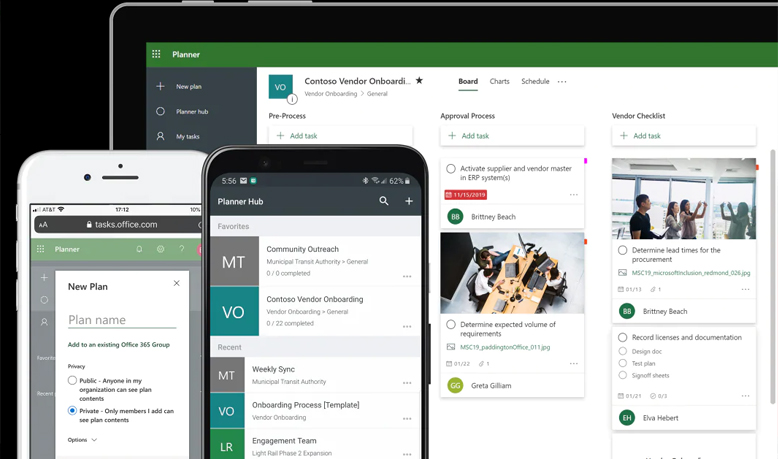
Do you manage groups of people but have a hard time keeping track of everything? Well, Microsoft has the tool for you! Microsoft Planner is a great application that is part of the Office 365 offering. It is a work in progress from Microsoft but none the less, Planner is a vast improvement from a simple to […]
Phishing Attacks In The Real World

When was the last time you almost lost $23,000 to a phishing email? This nearly happened to one of our clients this week. Fortunately, this phishing attempt was spotted before the funds were transferred, however, there are a few good lessons to take away from this story and we want to educate you so […]
Harden Employees Against Ransomware With KnowBe4

Are you curious to see who in your company is most likely to download a virus on your network? Well now you can find out and the best part is, its free. With KnowBe4 you can administer a range of free tools that will allow you to see which of your users is most likely fall for phishing […]
Repair Windows 10 With Windows Automatic Repair Tool

If you are having a problem with your desktop or laptop computer such as a reboot loop, corrupt Windows files, corrupt registry keys, corrupt registry driver or other Windows boot related issues you can resolve most of these by using the Windows Automatic Repair tool. Windows Automatic Repair or Startup Repair can fix a lot […]
CamStudio Screen Recording

If you have tried to explain a complex computer problem to your technical support group and found it difficult to bridge the gap between English and all the technical jargon, you may find it easier to make a screen recording of the problem rather than sending a lengthy email. CamStudio is a great, free program […]
Learn how to use a VPN
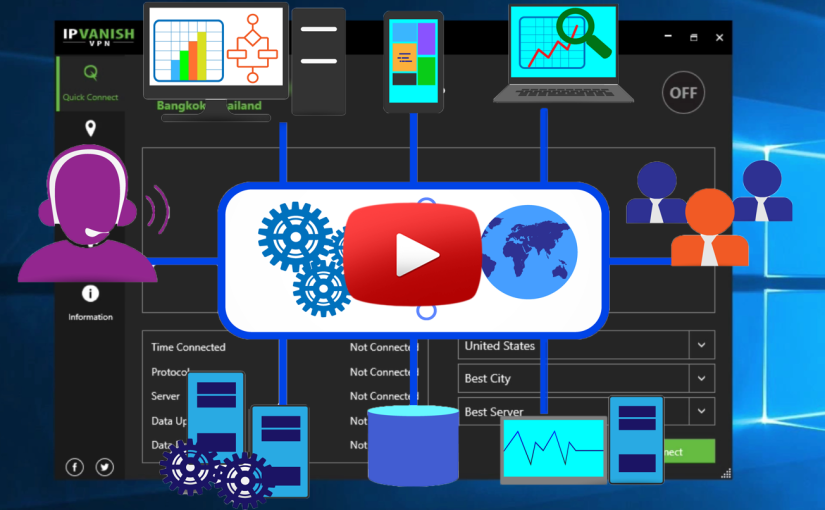
You may have heard of, or even used, a virtual private network (VPN), but do you know what it is? A VPN is an encrypted tunnel through a wide area network (WAN), also known as the Internet. This means that the network does not have to be located in one physical location, unlike a local area network (LAN). […]
Microsoft OneNote for Beginners
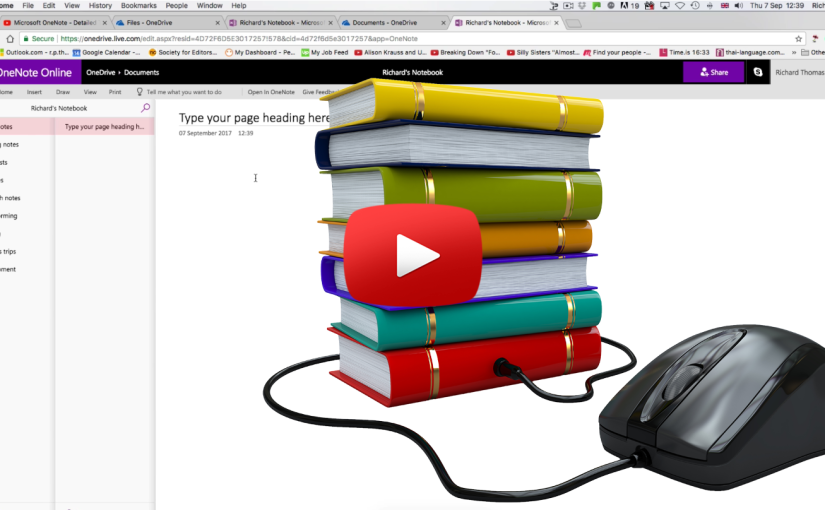
Are you aware of all the applications that come with your Microsoft Office 365 subscription? Most people think of Office 365 as a hosted email service but don’t realize that it is much more than that. Depending on the subscription that you have, almost every Office application that Microsoft offers will be included and is […]
Automate using Automate.io and Microsoft Flow

Business today gets done through the technology that connects us. The problem is that no matter what, there will never be one master program that does everything we specifically need. We’re forced into optimizing our work lives through no less than a dozen applications that we ourselves string together. While this is still faster than […]
Stop Ransomware In It’s Tracks

Today we are going to review a brilliant tool that stops ransomware and other spam in its tracks. It’s called Sendio Opt-Inbox, and it’s more than just antivirus and spam filtering; it’s all of that combined with two-factor authentication, meaning that if anyone sends you an email, a human has to verify that they sent that email to […]
Phishing For Passwords
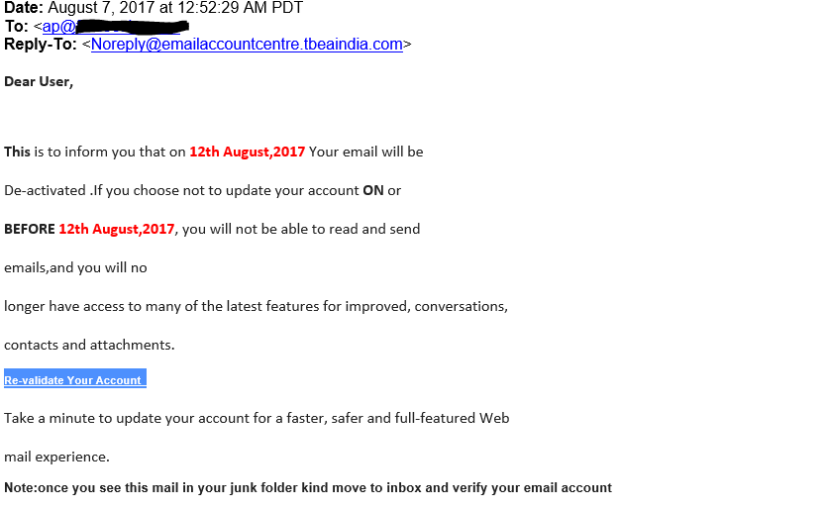
There has been a recent increase in phishing attempts across the US and it is concerning for many reasons. It is important to be aware of these issues and how these phishing attempts work so that you can protect yourself and your company. The unfortunate truth is that there is only so much you can do to […]
