Link Gmail and Outlook in Windows 10 Mail App
Like most people you probably have more than one email account. You can’t get away without having a personal email address and you likely have to manage one for work as well. All this and you also have to manage each of these accounts across your desktop, laptop and probably a handful of mobile devices. […]
Phishing Attacks In The Real World

When was the last time you almost lost $23,000 to a phishing email? This nearly happened to one of our clients this week. Fortunately, this phishing attempt was spotted before the funds were transferred, however, there are a few good lessons to take away from this story and we want to educate you so […]
Harden Employees Against Ransomware With KnowBe4

Are you curious to see who in your company is most likely to download a virus on your network? Well now you can find out and the best part is, its free. With KnowBe4 you can administer a range of free tools that will allow you to see which of your users is most likely fall for phishing […]
Microsoft OneDrive For Beginners
Every Microsoft product is designed to drive collaboration and efficiency. Microsoft OneDrive is no exception. Built as a solution to match the emergence of products like DropBox, OneDrive is integrated into the Office 365 offering and works seamlessly with all Microsoft Office products. In this video, we will show you how to access and set […]
Use Chat For Internal Business Communication
Email was once considered the hub of communication for business, and for external correspondence, it generally still is. However, if you just need to have a quick conversation with someone on the other side of the office, email is clunky and slow. Fortunately, there is a new trend for internal business communication: chat services. There are a […]
Phishing For Passwords
There has been a recent increase in phishing attempts across the US and it is concerning for many reasons. It is important to be aware of these issues and how these phishing attempts work so that you can protect yourself and your company. The unfortunate truth is that there is only so much you can do to […]
Use Technology To Avoid Pesky Salesmen

Technology has driven a wedge into the profession of sales in a way that industry wasn’t prepared to deal with. On the one hand, you rely on it to keep you connected, but on the other hand, you also want it to protect you and keep your life private as well. Salesmen look to utilize […]
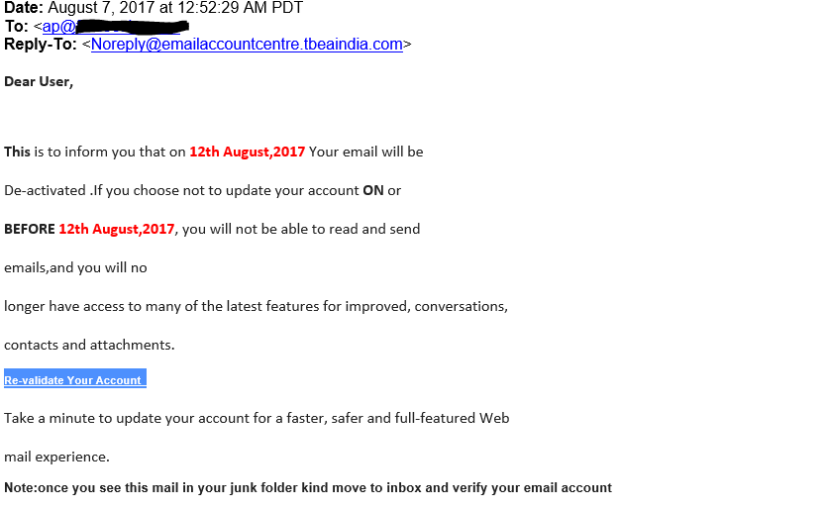
Scam Email and Phishing Attempts
As an IT support company, we are always telling our friends and clients to be cautious with what they click on or whom they give personal information to. Most people know to avoid giving money to a Nigerian price, but scams and phishing attempts are becoming more advanced every day. Many scam emails disguise themselves as people […]
Microsoft Outlook 2016 Task and ToDo Lists
One feature that frequently goes overlooked in Microsoft Outlook 2016 is the task feature. If you need a to-do list or a task list, you are probably more likely to find a third party tool rather than using the one that is built into Outlook. This feature works well, but is little known even among […]
Microsoft Outlook 2016 – How to create an email signature
Everyone needs an automatic signature in their email. Setting one up is a simple process if you follow the steps in this how-to video. Generally, an email signature is made up of your name, job title, company name, phone number(s), extension, website, and reply email address. The important thing to consider is how much information […]